Velocity Arc Start 480-481-1843 Inspiring Caller Verification

Inspiring Caller Verification combines real-time metadata, voice profiling, and behavioral analysis to curb impostor calls while preserving user autonomy. The approach emphasizes calm verification, cross-checking numbers, and avoiding rushed disclosures. For businesses, standardized protocols and transparent disclosures foster trust and accountability. The framework aims for secure, trusted exchanges with clear expectations. It offers a balanced path that invites scrutiny—and a closer look at how these practices reshape everyday communications.
What Is Inspiring Caller Verification and Why It Matters
Inspiring caller verification refers to methods that confirm a caller’s identity before proceeding with sensitive actions or data sharing. The approach centers on empowering individuals through reliable processes and clear expectations. It highlights how verification technology supports secure, trusted interactions, reducing impostor calls while preserving freedom to engage. Effective protocols balance accessibility with protection, ensuring legitimate voices remain confident and protected.
How Modern Verification Tech Detects Imposter Calls
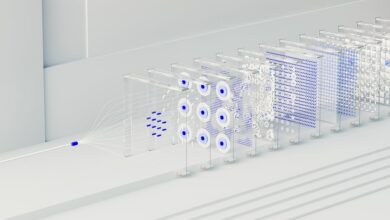
Modern verification technologies detect imposter calls by analyzing caller metadata, voice characteristics, and behavioral patterns in real time. They compare live signals against trusted profiles to assess caller legitimacy, flag anomalies, and prompt verification when risk indicators rise.
This approach strengthens autonomy by reducing unwanted intrusion while preserving user freedom, enabling confident decisions through rigorous imposter detection and transparent process controls.
Practical Steps for Individuals to Verify Incoming Calls
The approach emphasizes verification techniques, encouraging calm verification of caller identity, cross-checking numbers, and avoiding rushed disclosure.
It also foregrounds caller education, enabling users to recognize red flags, document suspicious activity, and confidently disengage when authenticity cannot be confirmed.
Best Practices for Businesses to Build Trusted Caller Interactions
Businesses can establish trusted caller interactions by implementing standardized verification protocols, robust identity checks, and transparent disclosure practices that collectively reduce the risk of impersonation and fraud.
The approach emphasizes Inspiring verification processes and durable Trusted interactions, enabling swift risk assessment, clear caller expectations, and measurable accountability.
When aligned with policy, these practices foster security, trust, and freedom in customer communication ecosystems.
Conclusion
Inspiring caller verification represents a prudent fusion of technology and user empowerment, fostering safer, more transparent interactions. By combining real-time metadata, voice profiling, and behavioral cues, it reduces impostor attempts while preserving user autonomy. Businesses gain trust through standardized protocols and clear disclosures. For individuals, a calm, methodical verification process becomes second nature. Example: a bank thwarted a phishing attempt when a customer cross-checked a caller’s number against official records and paused before disclosing sensitive data.